by houstonunitedcomputer.com
Share
by houstonunitedcomputer.com
Share
What Is Secure Data Destruction?
Secure data destruction is the process of permanently deleting or destroying data so it cannot be recovered.
It ensures that sensitive information is completely erased from devices before disposal, recycling, or reuse.
In simple terms, deleting files is not enough. When you press “delete,” the data still exists in the background. Secure destruction removes it completely—even from advanced recovery tools.
This process is a critical part of IT Asset Disposition (ITAD), where companies safely manage old or unused IT equipment.
Why Is Secure Data Destruction Important?
Secure data destruction protects your business from data breaches, legal risks, and reputational damage.
Without it, sensitive data can easily fall into the wrong hands.
Here’s why it matters:
- Data breaches are rising: According to IBM, the average cost of a data breach reached $4.45 million in 2023.
- Old devices still contain data: A NAID study found that 40% of used devices still had recoverable data.
- Legal compliance is strict: Regulations like GDPR and HIPAA require proper data disposal.
If data is leaked from discarded devices, companies can face the following:
- Heavy fines
- Loss of customer trust
- Legal consequences
That’s why secure data disposal is not optional—it’s essential.
What Is IT Asset Disposition (ITAD)?
ITAD is the process of safely disposing, recycling, or reusing old IT equipment.
It includes data destruction, asset tracking, and environmental compliance.
Businesses regularly upgrade:
- Laptops
- Servers
- Hard drives
- Mobile devices
Without ITAD, these devices can become a major security risk.
A strong ITAD strategy ensures the following:
- Data is destroyed securely
- Devices are handled responsibly
- Compliance requirements are met
What Are the Most Common Data Destruction Methods?
There are several secure data destruction methods, each designed for different devices and use cases.
The right method depends on data sensitivity, device type, and whether reuse is needed.
Let’s break them down.
1. Data Wiping and Overwriting
Data wiping overwrites existing data with random sequences, making it unreadable.
It is the most common and cost-effective method.
This method:
- Uses software tools
- Writes 1s and 0s over data
- Follows standards like NIST 800-88
👉 Best for:
- Reusing devices
- Selling old hardware
- Internal redeployment
2. Degaussing
Degaussing uses a powerful magnetic field to erase data permanently.
It disrupts the magnetic structure of storage media.
Important facts:
- Works only on magnetic devices (HDDs, tapes)
- Does NOT work on SSDs
- Makes the device unusable
👉 Best for:
- High-security environments
- End-of-life devices
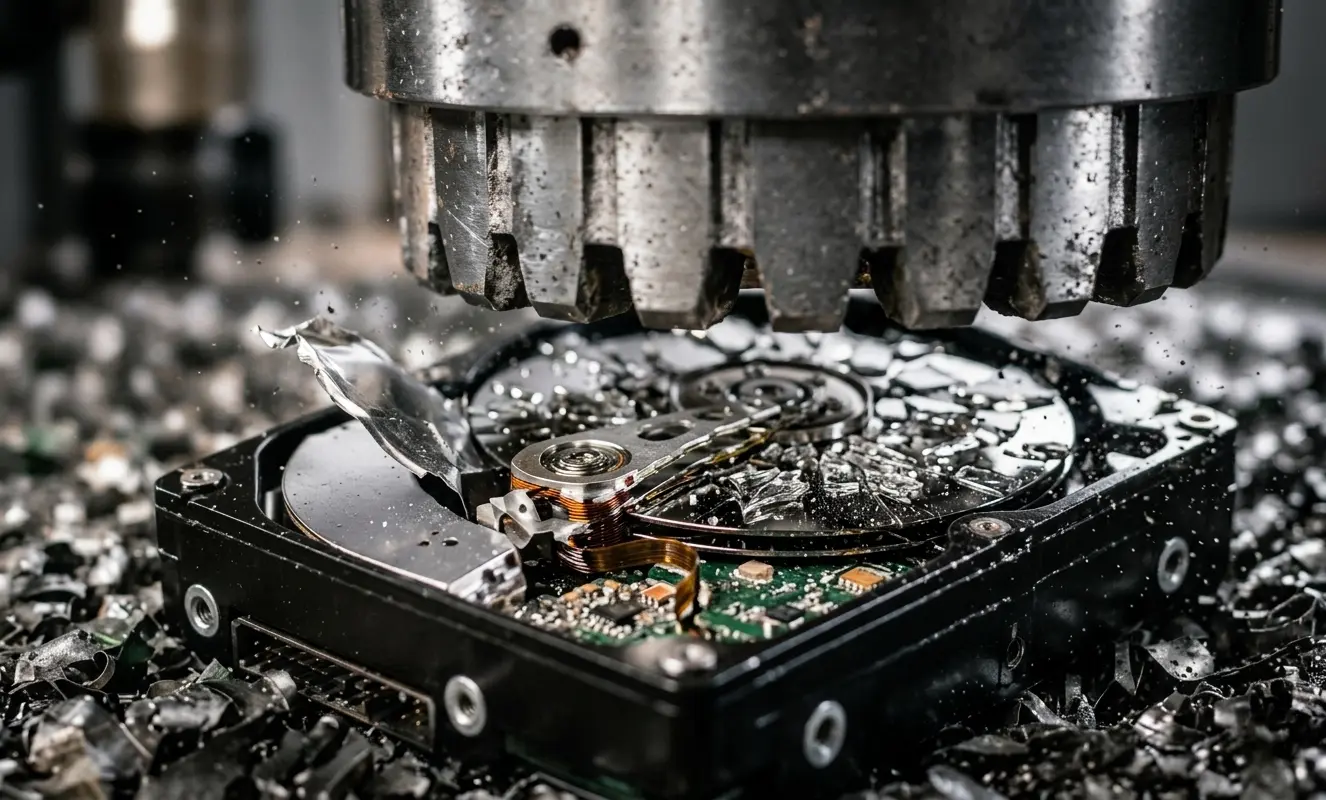
3. Physical Destruction (Shredding)
Physical destruction completely destroys storage devices so data cannot be recovered.
This includes shredding, crushing, or drilling.
This method:
- Destroys hardware physically
- Provides maximum security
- Eliminates reuse value
👉 Best for:
- Highly sensitive data
- Damaged or failed drives
4. Cryptographic Erase
Cryptographic erase deletes encryption keys, making data unreadable instantly.
It is fast but depends on proper encryption.
👉 Best for:
- Encrypted systems
- Modern enterprise environments
5. Built-In Device Sanitization (SSD)
Modern SSDs include built-in secure erase commands.
These are designed specifically for flash storage.
👉 Important:
- SSDs behave differently than HDDs
- Regular wiping may not be effective
Data Wiping vs Physical Destruction: Which Is Better?
Data wiping preserves hardware value, while destruction guarantees maximum security.
The best choice depends on your goals.
| Method | Security | Reuse | Cost |
|---|---|---|---|
| Wiping | High | Yes | Low |
| Destruction | Maximum | No | Higher |
👉 Key Insight:
Many companies unnecessarily destroy devices, losing thousands in resale value.
What Are Data Destruction Standards and Compliance Requirements?
Data destruction standards ensure that data is erased securely and legally.
Following them protects your business from fines and risks.
Key Standards:
- NIST SP 800-88 – Recommended by the U.S. government
- DoD 5220.22-M – Military-grade wiping method
- GDPR – Data protection law in Europe
- HIPAA – Healthcare data protection
👉 Fact:
Regulators don’t just ask “Did you delete data?”
They ask: “Can you prove it?”
What Is a Certificate of Data Destruction?
A Certificate of Data Destruction is proof that your data was securely erased or destroyed.
It is essential for audits and compliance.
It typically includes:
- Device serial numbers
- Destruction method
- Date and time
- Technician details
Without this certificate, your business remains exposed.
What Is Chain of Custody in Data Destruction?
Chain of custody tracks the movement of devices from collection to destruction.
It ensures no data is lost, stolen, or accessed during the process.
This includes:
- Secure transportation
- Controlled handling
- Audit logs
👉 This is critical for compliance and legal protection.
Common Mistakes in Data Disposal (And How to Avoid Them)
Most businesses think deleting files or factory resetting devices is enough—it’s not.
These mistakes can lead to serious data breaches.
❌ Mistake 1: Deleting Files Only
✔ Fix: Use certified data wiping tools
❌ Mistake 2: Factory Reset
✔ Fix: Perform verified data sanitization
❌ Mistake 3: Throwing Devices Away
✔ Fix: Use professional ITAD services
❌ Mistake 4: No Documentation
✔ Fix: Always get a destruction certificate
Best Practices for Secure Data Destruction
Following best practices ensures your data remains protected and compliant.
✔ Create a Data Disposal Policy
Define clear rules for handling old devices
✔ Classify Data Sensitivity
Not all data needs the same level of security
✔ Choose the Right Method
Match method to device type
✔ Work with Certified Vendors
Look for R2, ISO, or NAID certifications
✔ Maintain Records
Always document the process
Why Businesses Should Use Professional ITAD Services
Professional ITAD providers ensure secure, compliant, and efficient data destruction.
They reduce risk while saving time and resources.
Benefits include:
- Certified processes
- Audit-ready documentation
- Secure logistics
- Environmental compliance
👉 Real-world example:
Morgan Stanley was fined $35 million due to improper data disposal.
That’s the cost of doing it wrong.
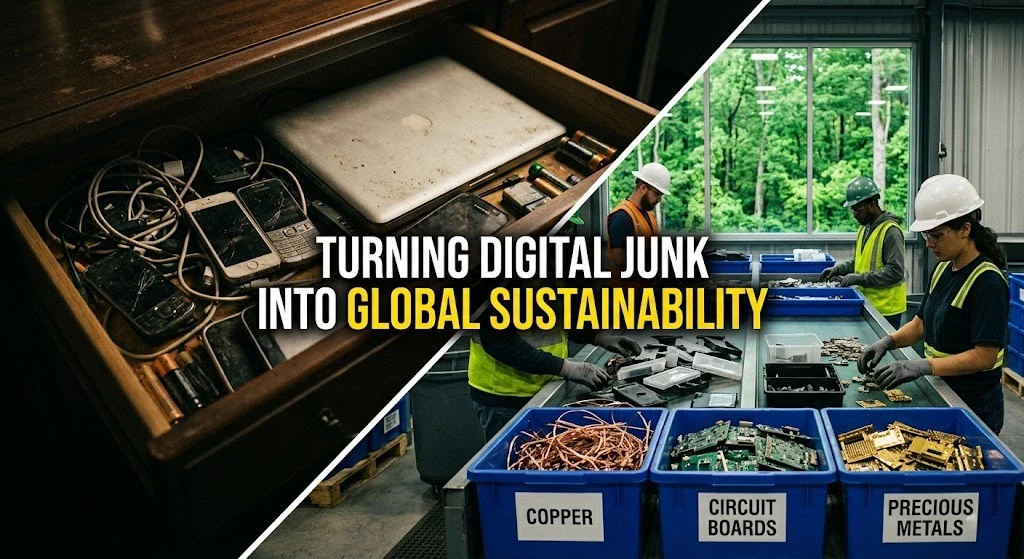
How Secure Data Destruction Supports Sustainability
Secure data destruction doesn’t mean destroying everything.
Smart businesses focus on reuse and recycling.
Benefits:
- Reduces e-waste
- Saves costs
- Supports ESG goals
👉 Fact:
The world generates over 50 million tons of e-waste annually (Global E-waste Monitor).
Reusing devices after secure wiping helps reduce this.
Final Thoughts: Secure Data Destruction Is a Business Necessity
Secure data destruction is not just an IT task—it’s a business risk strategy.
Done right, it protects data, ensures compliance, and saves money.
The key takeaway:
- Wipe when you can
- Destroy when you must
- Always verify and document
If your business handles sensitive data (and it does),
Then secure data disposal is something you cannot ignore.
STAY IN THE LOOP